To See Farther, Let’s Stand on the Shoulders of Giants
Part 3 of My Series: 50 Mental Models to Think Like a High-Level Generalist
I want to see as far as possible, so I try to stand on the shoulders of giants.
You can find the first 5 here.
Let’s go.
Law: Stare Decisis Et Non Quieta Movere
The Big Idea
“Stand by the thing decided and do not disturb the calm.”
In plain English: past decisions become the default rule for similar cases, that’s how case law gets built.
More precisely:
A court’s prior decision is a precedent.
Stare decisis is the principle that courts should follow relevant precedents.
When a court rules on a novel case, it creates an anchor point that judges, lawyers, and citizens will align around.
Precedent is therefore a tool:
a arbitrary tool for deciding when reality is new and uncertain,
that creates predictability by imposing a default for future similar situations.
Arbitrary, yes, but effective for managing uncertainty at low cost.
The Mental Model
Once again, the trick here isn’t in generalizing, it’s in transposing.
Our first reaction to a new situation tends to become our “precedent”: the default response next time.
We can thank biology and psychology for that:
Similar causes (context), similar effects (reactions).
Our brains are wired to lock in a solution fast (anchoring, confirmation, availability).
So the right question, every time you face something for the first time, isn’t “what should I do now?” but: “Am I okay with this becoming my standard?”
If, on your first investment:
You require yourself to read the latest annual report + transcripts before buying, you create a standard.
You buy because your colleague won’t stop talking about it, you also create a standard, but a bad one.
Applying this mental model with zeal is an excellent way to deserve it until you get it. Especially the “until” part.
The 1-Line Rule
Choose your reaction to a new situation as if you’ll have that same reaction every time, because you probably will.
Biomimetics: Meta Mental Model
The Big Idea
Congratulations, it’s a meta mental model! → A mental model that lets you discover (or create, your choice) other mental models.
Based on its definition, biomimetics is a core discipline in this series:“Biomimetics is the emulation of the models, systems, and elements of nature for the purpose of solving complex human problems.”
The idea of “mental models” fits naturally inside biomimetics, with one difference: mental models (and therefore this series) aren’t limited to nature in the biological/ecological sense, but in the physical sense (our universe, and beyond).
If we stick to a biological definition, nature is (roughly) just the result of an initial event, environmental variation, and natural selection, that is:
the selection of traits that appeared by chance through mutations and that maximize survival and reproduction, and
the disappearance of the rest.
Natural selection is therefore a machine for creating (or selecting, your choice) increasingly optimized processes.
Put differently: among all the possibilities the universe offers, natural selection will select the most effective ones (for a given environment).
That makes it an excellent source of mental models to shamelessly clone.
The Mental Model
As a meta mental model, the process is only meant to discover other mental models (some people call that meta-wisdom):
Study biological/ecological processes shaped by natural selection, and understand why they’re so effective;
Describe and recognize the situations in which that process is effective;
Apply the process in similar situations.
Jeff Bezos has admitted to “stealing” ideas from biology to build Amazon. His shareholder letters contain clear examples.
For a complete, step-by-step case study → Mental Model #6: Clonal Selection.
The 1-line Rule
Steal proven solutions from nature: identify the function, extract the principle, then port it to your problem.
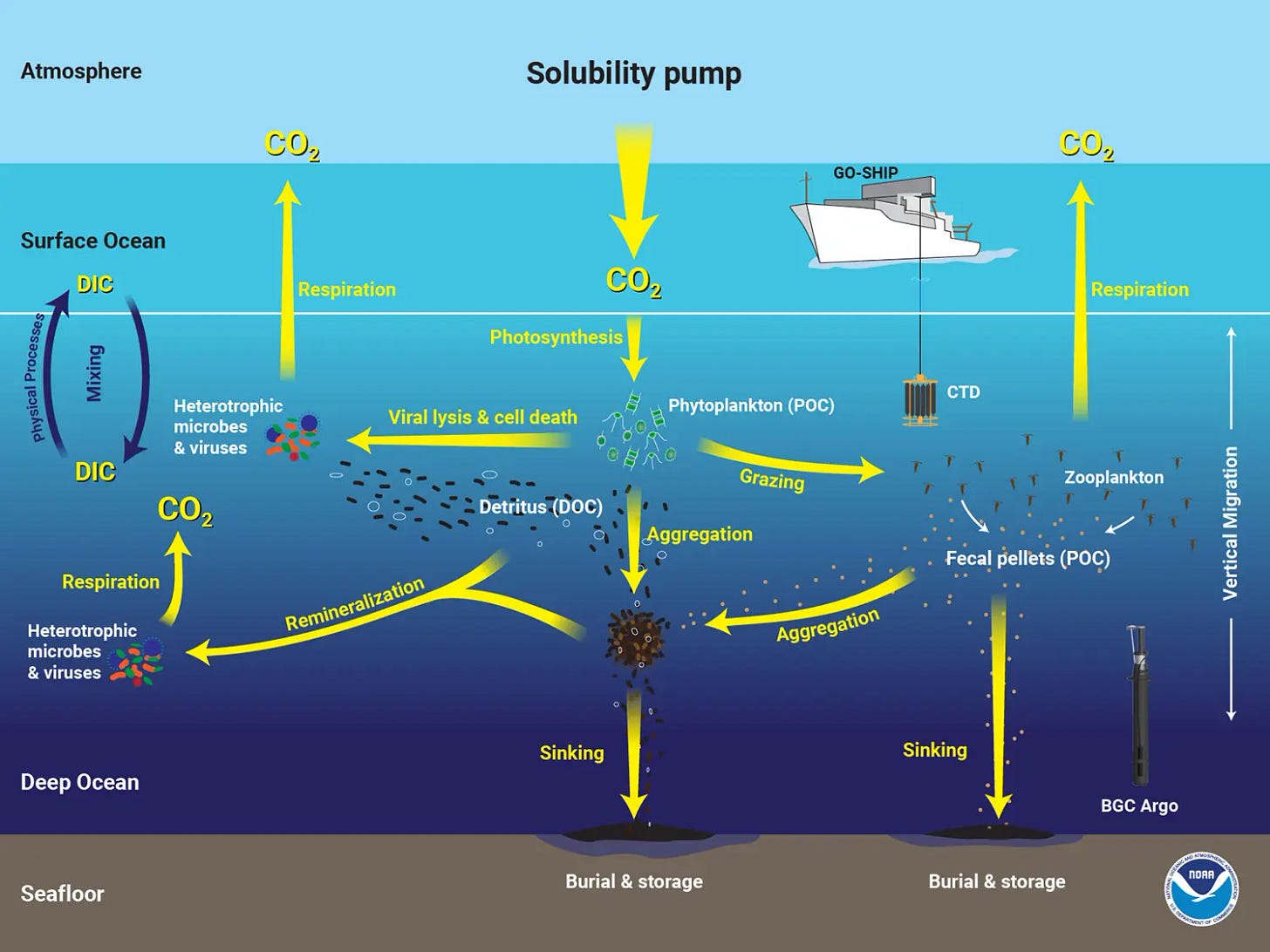
Oceanography: Reservoir Thinking
The Big Idea
The ocean is best understood as a system of stocks and flows:
a stock = a quantity contained in a compartment → CO₂ in the deep ocean, salt at the surface, etc.
a flow = a transfer between compartments → CO₂ from the deep ocean to the atmosphere.
The key feature here is that, in oceanography, we often deal with gigantic stocks relative to the flows that change them.
The direct consequence is inertia: even if flows change today, the stock moves slowly.
Very slowly. For example:
A hot summer can raise the temperature of the top 50 meters in a few days/weeks.
But then heat takes years to penetrate below the surface (thermocline), and decades, or even centuries, to reach (and meaningfully alter) the deep ocean.
That response time becomes the oceanographer’s nightmare: it drastically complicates the analysis of causes and their consequences.
The Mental Model
The goal is to look for similar structures, estimate their response time, and adapt our strategy to the system’s timeframe.
Identify the Stock: what variables “carry” the system? (cash, backlog, trust, love, etc.).
Identify the Flows: what flows change the stocks?
Estimate the Response Time: a workable approximation is response time ≈ stock / net flow (more often a mental estimate than a real calculation).
Don’t misread noise: if response time is long, short-term variations are mostly noise.
WARNING: a flow is bidirectional along the same axis, and its speed can differ wildly in each direction. Think reputation: it can take decades to (re)build (high stock & low flow), but get destroyed in seconds (high stock & very high flow).
The 1-Line Rule
Higher Stocks + Lower Flows = Higher Response Time → Higher Relevant Timeframe
Cybersecurity: The Best Defense Is Offense
The Big Idea
Cybersecurity is war. And like any war, it’s won through paths.
A system doesn’t fall “because it’s imperfect.” It falls because there exists a path with a positive attack ROI:
an entry (e.g., reused password),
followed by a viable path to the target (a chain of access all the way to the keys to the kingdom),
an impact (money, data, reputation, etc.).
Cybersecurity is the art of finding and blocking those paths, and of limiting the blast radius when it still gets through.
That’s why engineers practice pentesting (penetration testing) with zeal: simulating an attack yourself to find those paths and block them.
As often with systems (yes, them again), the practice generalizes extremely well (a country, a portfolio, an economy, an industrial process, etc.).
The Mental Model
Pentesting happens in 5 phases:
Reconnaissance → Gather all available information.
Fundamentals, drivers, correlations, liquidity, dependencies, history, maturities, etc.Scanning → Map the attack surface and identify breaking points.
Concentration (sector, geography, currencies, etc.), implicit leverage, counterparties, correlation spikes, etc.Exploitation → Test scenarios step by step until they cause real damage.
Historical FX moves (-20% on EURUSD) / needing day-to-day liquidity + deep drawdowns, etc.Post-Exploitation → Assess potential damage and its probabilities.
The € has already dropped 15% per year versus the $ for multiple years in a row. As a European investor invested only in USD-denominated assets, my annual performance can be wiped out by FX.Reporting & Remediation → Turn discoveries into path-blockers.
I diversify my currency exposure / I keep 6 months of expenses + taxes in cash / I stagger my options maturities by at least 6 months, etc.
The 1-Line Rule
Without an adversary model, you build a random defense that leaves the cheapest entry point wide open.
Political Science: State Capacity
Power is useless if you don’t have the capacity to wield it.
That capacity is called state capacity.
More formally, it’s: the ability of governments to effectively implement their policies and achieve their goals.
For a government, that capacity comes from the capacity of its organizations (police, tax administration, teachers, etc.) and its infrastructure (police stations, online tax portals, schools, etc.).
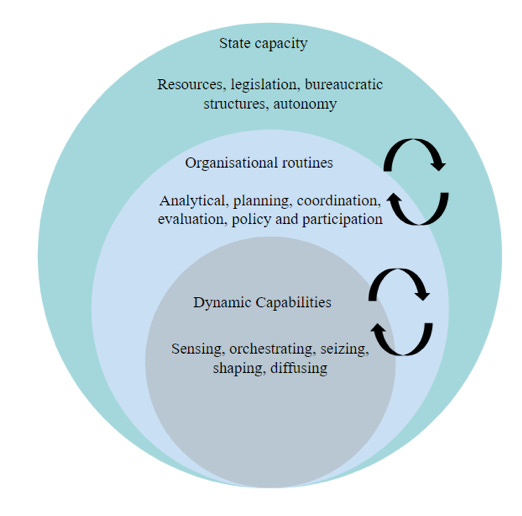
But you can generalize this principle to any structure made of living beings with power asymmetries: a family, a classroom, a city, etc.
The Mental Model
The “state capacity” reflex is to explicitly separate the power to decide from the capacity to execute, to enforce, and to prevent.
When a new leader arrives (CEO, head of state, president of a regulatory body, etc.), the question isn’t “what does he want?” but:
is the system he runs capable of executing what they want, and
where is the potential bottleneck?
When Gary Gensler, former “Blockchain & Money” instructor at MIT, took over the SEC in 2021, the crypto community welcomed him like a near messiah.
But what followed illustrated the mental model perfectly: the SEC became crypto’s worst enemy during the Biden administration, and Gary Gensler was shaped by the SEC system more than he shaped it.
The appointment of Kevin Warsh as the next Fed Chair could potentially be a concrete case study for applying this mental model.
The 1-Line Rule
In every system, the real ruler isn’t the top, it’s the bottleneck. Weak capacity yields promises, strong capacity yields consequences.
Only 35 more to go. The pace is very intense, but this series is transformative.
Every week I feel a massive step-change in progress. No doubt I’ll be far better equipped at the “end” of this series.
I hope it’s the same for some of you. Either way, I’m trying.
Take care,
Masters of Compounding
Scheduling Update:
I’m changing the publishing schedule for my series, 50 Mental Models to Think Like a High-Level Generalist.
The original plan was one post per week for ten weeks. In practice, that pace is too constraining to maintain the level of quality I’m aiming for.
So I’m giving myself full flexibility on timing. I’ll publish the series either as one complete post or split into two posts, released as soon as they’re ready. I won’t give a precise date, but it won’t be finished for at least a few months.
To be clear: this isn’t a stop. I’m working on it continuously and will keep doing so. I just enjoy writing this series too much to ruin it with arbitrary deadlines that hurt the quality.
Thanks for your understanding.
Take care.
DISCLAIMER:
I’m not a domain expert in every field I’m drawing from. I’m simply an investor with a lot of curiosity, and a lot of time to feed it. If you spot an empirical error or want to add nuance, I’d welcome corrections, my goal is accuracy and usefulness.
If you’re an expert in any domain, WHATEVER IT IS, and you have a “big idea” that generalizes well, please don’t hesitate to suggest it. Drop it in the comments, DM me, or write a note and tag me, I’d genuinely love to include it. Of course, I’ll credit you in the post.
Source
Law: Stare Decisis Et Non Quieta Movere
I have no doubt a legal specialist might be slightly offended by how much I simplified stare decisis and precedent. But it was a necessary tradeoff for readability. For a more complete and rigorous definition:
Cornell Law School (LII, Wex) — “Stare decisis”.
Cornell Law School (LII, Wex) — “Precedent”.
To go deeper on the behavioral side of “precedent”:
Tversky & Kahneman — “Availability: A Heuristic for Judging Frequency and Probability” (Cognitive Psychology, 1973).
Tversky & Kahneman — “Judgment under Uncertainty: Heuristics and Biases” (Science, 1974).
Biomimetics: Meta Mental Model
On Bezos, biology, and business: Jeff Bezos (Amazon), 2006, 2016, and 2020 Letter to Shareholders.
For a concrete biomimetics case study: Julian F. V. Vincent et al., “Biomimetics: its practice and theory,” Journal of the Royal Society Interface (2006).
Oceanography: Reservoir Thinking
A relatively gentle introduction: NOAA Climate.gov, Climate Change: Ocean Heat Content.
A more complex and more specific approach (and nothing beats a concrete case to highlight real-world complexity): Messias et al., 2022, The redistribution of anthropogenic excess heat is a key driver of warming patterns in the North Atlantic.
Cybersecurity: The Best Defense Is Offense
My source for the pentest methodology. Note: I merged/removed some steps to make the framework generalizable: PTES, The Penetration Testing Execution Standard.
For those interested in cybersecurity but not experts (like me): an excellent guide that goes deep while staying approachable. It felt like reading a modern-day Art of War: NIST, SP 800-115: Technical Guide to Information Security Testing and Assessment (2008).
Political Science: State Capacity
For this mental model, a single (excellent) source was enough. It breaks down state capacity from every angle: Cingolani (2013), “The State of State Capacity: a review of concepts, evidence and measures.”